National Security — The 2026 LeT Trans-Border Module and India’s Urban Vulnerabilities
Introduction
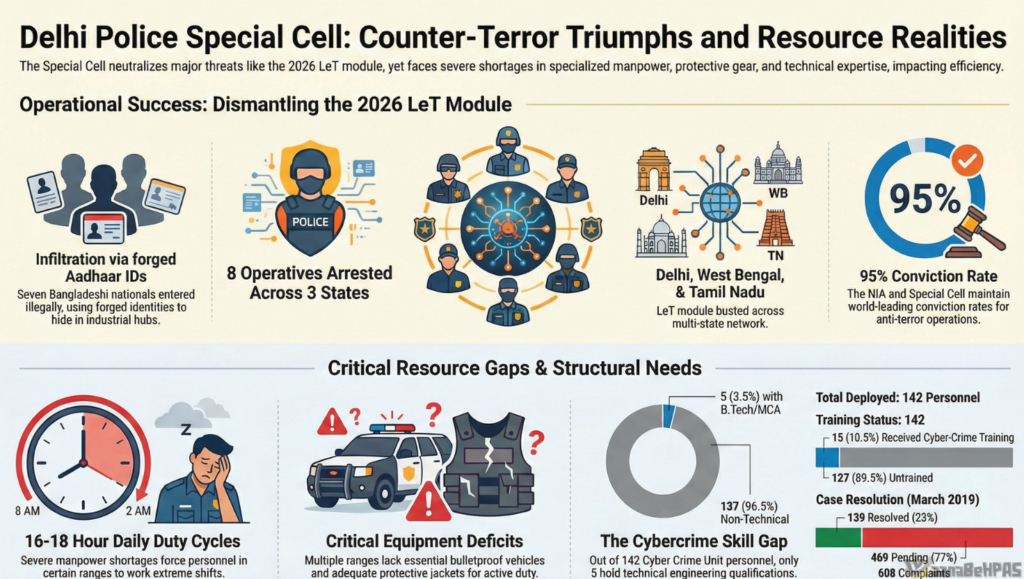
In February 2026, the Special Cell of the Delhi Police dismantled a sophisticated terror module linked to the Pakistan-based outfit Lashkar-e-Taiba (LeT). The multi-state operation, spanning West Bengal and Tamil Nadu, not only prevented a potential high-impact strike in the National Capital Region but also exposed a new operational doctrine in cross-border terrorism: deep-cover urban embedding through migrant industrial corridors.
For UPSC aspirants, the episode offers critical insights into internal security, cross-border terrorism, intelligence coordination, urban vulnerabilities, identity fraud, and institutional preparedness.
1. Operational Overview: From Psy-Ops to Multi-State Crackdown
Trigger Event: Poster-Based Psychological Operation (Psy-Op)
On February 8, 2026, pro-terror posters were found at Janpath Metro Station and nearby areas in Delhi. The posters contained inflammatory slogans and images of slain militants, attempting to provoke communal unrest and test operational capabilities.
Rapid CCTV triage and digital forensics enabled investigators to trace suspect movements across state lines.
Timeline of Arrests
- February 15, 2026 – Two operatives arrested in Kolkata.
- February 21, 2026 – Six additional suspects apprehended in Tiruppur, Tamil Nadu.
- Total arrests: Eight suspects, including seven Bangladeshi nationals allegedly using forged Indian identity documents.
Strategic Context
The crackdown occurred months after a major car explosion near the Red Fort in November 2025, which heightened national alert levels and indicated renewed aggression by Pakistan-based proxies.
2. Command & Control Architecture: Remote Handling Model
The Handler: Shabir Ahmad Lone
The module was allegedly directed by Shabir Ahmad Lone, also known as “Raja” or “Kashmiri.”
Profile Highlights:
- Native of Srinagar (Kangan).
- Arrested in 2007 with arms cache.
- Released in 2018 from Tihar Jail.
- Subsequently relocated to Bangladesh.
- Linked to LeT leadership networks.
Key Features of the Command Structure
- Remote Direction from Foreign Jurisdiction
- Exploits jurisdictional friction between South Asian agencies.
- Ensures plausible deniability.
- Encrypted Communication
- Operatives sent “Proof of Act” videos.
- Handler verified tasks in real-time.
- Decentralized Execution
- Field leader (Umar Faruk) managed Indian operations.
- Digital vetting before recruitment.
UPSC Link:
GS Paper III – Role of external state and non-state actors in internal security challenges.
3. Logistical Innovation: Weaponizing Migrant Industrial Corridors
The “Tiruppur Strategy”




The module represents a tactical shift:
- Earlier infiltration routes: Punjab, Jammu & Kashmir.
- New strategy: Embedding in Southern industrial hubs (Tiruppur garment sector).
Why Tiruppur?
- High-density migrant workforce.
- Informal labor documentation.
- Anonymity within industrial clusters.
- Low suspicion compared to border zones.
Identity & Financial Concealment
- Forged Aadhaar Cards
- Legitimate blue-collar jobs to self-fund operations.
- No suspicious foreign remittances.
- Seized materials:
- 10 mobile phones
- 16 SIM cards
- 25 credit/debit cards
- 5 POS machines
This reveals a decentralized micro-financing ecosystem, reducing dependency on cross-border hawala routes.
UPSC Link:
GS III – Money laundering, terror financing, and cyber-security challenges.
4. Tactical Objectives: Reconnaissance & Potential Targets
Psychological Warfare
The February 6–7 mission involved:
- Poster placements at 10 locations.
- Filmed documentation for handler verification.
- Targeted propaganda referencing Kashmir and Pakistan.
Ironically, the digital footprint from these videos enabled investigators to trace the network.
Reconnaissance for Kinetic Attacks
Intelligence suggests surveillance of:
- Red Fort – Potential IED target.
- Gauri Shankar Temple – High-density religious site, especially during Mahashivratri.
The selection indicates:
- Symbolic targets.
- High footfall.
- Maximum psychological impact.
UPSC Link:
GS III – Security challenges in border areas and urban areas; critical infrastructure protection.
5. Institutional Vulnerabilities: Systemic Gaps in Counter-Terror Response
Findings Reflect Broader Concerns
According to audit observations (CAG Report No. 15 references):
(A) Manpower Deficit
- Required: 987 personnel.
- Available: 638.
- 16–18 hour duty cycles.
- Proposal to create “Eastern Range” pending for 4 years.
(B) Mobility Deficiencies
- 25 vehicles available vs 47 required.
- Shortage of bulletproof vehicles.
(C) Protection Gear Gap
- 105 bulletproof jackets for 506 personnel.
- ~79% operational force unprotected during interventions.
(D) Cyber Crime Unit (CCU) Weakness
- Only 5 technically qualified personnel out of 142.
- 469 pending complaints.
- Limited decryption capabilities.
Strategic Implication
Modern terror modules use:
- Encrypted apps.
- Decentralized SIM ecosystems.
- Digital payment layering.
Without cyber modernization, detection lag increases.
UPSC Link:
GS II – Governance and institutional capacity.
GS III – Cyber security and role of technology in internal security.
6. Broader Security Themes Emerging
1. Migration & Security Interface
Economic corridors can be exploited if identity verification is weak.
2. Aadhaar & Identity Fraud
Highlights need for stronger backend validation, not rollback.
3. Inter-State Intelligence Latency
Operatives staged in South India but targeted Delhi.
4. Foreign Jurisdictional Shielding
Handlers operating from Bangladesh illustrate need for deeper diplomatic-security cooperation.
7. Strategic Recommendations (UPSC-Ready Points)
Administrative Reforms
- Strengthen Special Cell manpower.
- Expedite Eastern Range creation.
- Improve duty-cycle management.
Cyber Modernization
- Recruit B.Tech/MCA specialists.
- AI-driven pattern recognition.
- Real-time encrypted traffic analytics.
Identity Governance
- Mandatory digital police verification in high-risk industrial corridors.
- Integration of immigration databases.
- Tech-enabled Aadhaar authentication strengthening.
Legal & Policy
- Strict enforcement of Immigration & Foreigners Bill (2025).
- Stronger terror financing tracking via FIU.
Urban Security Hardening
- Smart surveillance grids in heritage zones.
- Festival-season risk assessment models.
- Drone-based perimeter mapping.
Conclusion
The 2026 LeT module marks a paradigm shift from border infiltration to industrial embedding. Terror logistics are no longer confined to frontier zones; they are now concealed within India’s economic arteries.
The success of the February 2026 operation demonstrates:
- The importance of digital forensics.
- Inter-state coordination.
- Proactive intelligence policing.
However, the exposed institutional fatigue signals that counter-terror success must be institutionalized, not episodic.
For UPSC aspirants, this case is a textbook example of:
- Evolution of cross-border terrorism.
- Urban internal security vulnerabilities.
- Governance gaps in identity and cyber systems.
- Need for whole-of-government security architecture.